Sorry, this functionality is only available for verified hoteliers
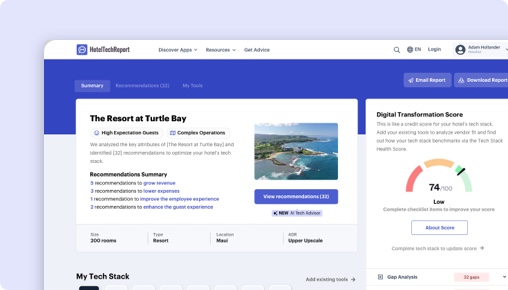
The project dashboard is a free tool that is only available to verified hoteliers to make adopting new technology easier by streamlining their research and simplifying their communication workflow.

Cyber Security & Fraud Prevention Software
By Jordan Hollander
Last updated on March 27, 2026
Jordan Hollander
CEO @ Hotel Tech Report
Jordan is the co-founder of HotelTechReport, the hotel industry's app store where millions of professionals discover tech tools to transform their businesses. He was previously on the Global Partnerships team at Starwood Hotels & Resorts. Prior to his work with SPG, Jordan was Director of Business Development at MWT Hospitality and an equity analyst at Wells Capital Management. Jordan received his MBA from Northwestern’s Kellogg School of Management where he was a Zell Global Entrepreneurship Scholar and a Pritzker Group Venture Fellow.
-
513
articles contributed
Our reviewers evaluate software independently. Learn how we stay transparent, read our review methodology, and tell us about any tools we missed.
This list is based on research we’ve conducted since 2017, analyzing dozens of Hotel Cyber Security & Fraud Prevention Software using verified hotelier reviews, product deep dives, and our proprietary HTScore.
At first glance, most fraud prevention and cyber security providers look similar. They all promise to reduce chargebacks, protect guest data, and detect threats in real time. But in practice, these solutions operate very differently. Some focus narrowly on payment fraud, others on IT security, and a growing group try to unify both into a single platform.
That’s where most hotels get stuck. The real challenge isn’t deciding whether you need protection, it’s figuring out what kind of protection you actually need and which type of provider is built for your operating model. Choosing the wrong approach can either leave gaps in coverage or create unnecessary complexity for your team.
To help you cut through that noise, we surveyed 2002 hoteliers across 47 countries and combined verified hotelier feedback with hands-on product demos. At Hotel Tech Report, we don’t just look at feature lists. We analyze how different types of solutions perform in real hotel environments and where they actually deliver on preventing losses.
We also layer in verified partner recommendations from hotels actively using these systems, so you can see not just what vendors claim, but which ones operators trust when real money and real risk are on the line.
This guide is designed to help you answer the questions that actually drive the decision:
What type of provider is the best fit for our hotel, payment-focused, infrastructure security, or an all-in-one platform?
Which solutions are actually proven to reduce chargebacks and fraudulent bookings in real operations?
Where do hotels like ours typically see the biggest gaps or risks?
Which platforms are easy to manage day to day, and which ones require constant oversight?
Who do other hoteliers trust when it comes to protecting revenue and guest data?
If you’re trying to make a confident decision in a category where everything sounds the same on paper, this guide will help you understand the different types of providers and use real hotel feedback and verified recommendations to find the solution that best protects your revenue and fits your operation.
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
Over 2M+ Leading Hotel Professionals Trust Our Advice











How We Evaluate Fraud Prevention Solutions
Cyber security and fraud prevention tools often look similar, but the real difference is how they perform in daily operations. At Hotel Tech Report, we evaluate solutions based on their ability to prevent revenue loss, reduce manual workload, and integrate cleanly into hotel systems. By combining verified hotelier reviews with hands-on analysis, we focus on what actually works in practice, not just what looks good on paper.
How we determine the types
Cyber security and fraud prevention solutions vary widely, but the differences that actually impact buying decisions tend to fall along a few core dimensions:
Scope of protection: whether the solution focuses narrowly on payments and fraud or broadly across infrastructure, data, and user activity
Control model: tools that are actively managed by hotel teams vs. those that automate detection and response with minimal intervention
Primary risk focus: financial fraud (e.g., chargebacks, payment abuse) vs. operational and data security (e.g., breaches, unauthorized access)
Integration depth: standalone tools vs. deeply embedded solutions within PMS, payment systems, and IT infrastructure
These vectors shape how hotels deploy, manage, and extract value from each type of solution.
Comparison Preview
Type | Primary Differentiator | Best For | Team Involvement / Control Model | Typical Integration Requirements | Tradeoffs |
|---|---|---|---|---|---|
Payment Fraud Prevention Platforms | Focus on transaction-level fraud and chargebacks | Hotels with high online booking volume | Revenue / Finance-led with rule tuning | Booking engine, payment gateway | Limited visibility beyond payments |
Network & Infrastructure Security Tools | Protect hotel systems, networks, and devices | Full-service hotels, resorts, IT-driven orgs | IT-led, ongoing management required | PMS, network infrastructure, endpoints | Complex to manage, less fraud-specific |
Identity & Access Management (IAM) Solutions | Control user access and prevent unauthorized entry | Multi-property groups, compliance-driven hotels | IT / Security-led with policy control | PMS, internal systems, staff tools | Narrow scope (access vs. broader threats) |
Unified Security & Risk Platforms | Combine fraud, data protection, and monitoring in one system | Enterprise portfolios seeking centralized control | Cross-functional (IT, Finance, Ops) | Deep integrations across tech stack | Higher cost, longer implementation |
Payment Fraud Prevention Platforms
These solutions are designed to detect and prevent fraudulent transactions, particularly in card-not-present environments common in hotel bookings.
Best fit for boutique hotels, urban properties, and any operation with high OTA or direct booking volume. Typically owned by Revenue Management or Finance teams.
Category | Details |
|---|---|
Definition | Focused tools that detect and prevent fraudulent transactions, especially for online and card-not-present bookings |
Typical Buyer | Revenue Manager, Finance Director, eCommerce lead |
Best Fit Properties | Boutique hotels, urban properties, high OTA or direct booking volume hotels |
Strengths | • Reduces chargebacks and fraudulent reservations• Real-time transaction risk scoring• Supports 3D Secure and tokenization• Easy to deploy within booking flows |
Tradeoffs | • Limited visibility beyond payments• Requires ongoing rule tuning• Does not address broader cyber threats |
When It’s the Wrong Fit | • Hotels needing full IT security coverage• Properties with low online transaction volume |
Network & Infrastructure Security Tools
These platforms focus on securing the hotel’s IT environment, including networks, servers, devices, and endpoints.
Best suited for large full-service hotels, resorts, and properties with complex IT infrastructure. Typically owned by IT teams or managed service providers.
Category | Details |
|---|---|
Definition | Solutions designed to secure hotel networks, systems, and devices from cyber threats like malware and unauthorized access |
Typical Buyer | IT Director, Head of Infrastructure, Managed Service Provider |
Best Fit Properties | Full-service hotels, resorts, large properties with complex IT environments |
Strengths | • Protects against malware, ransomware, and intrusions• Secures guest Wi-Fi and internal systems• Continuous vulnerability monitoring• Supports compliance requirements |
Tradeoffs | • Requires technical expertise to manage• Less focused on payment fraud• Resource-intensive for smaller teams |
When It’s the Wrong Fit | • Hotels without dedicated IT resources• Teams primarily focused on fraud/chargebacks |
Identity & Access Management (IAM) Solutions
IAM solutions control who has access to what systems, reducing the risk of unauthorized access and internal breaches.
Best for multi-property groups and organizations with large or distributed teams. Typically managed by IT or Security.
Category | Details |
|---|---|
Definition | Tools that manage and control user access to systems, reducing risk of unauthorized access and internal breaches |
Typical Buyer | IT Security Lead, Compliance Officer, HR (for access governance) |
Best Fit Properties | Multi-property groups, branded hotels, organizations with large or distributed teams |
Strengths | • Centralized access control across systems• Reduces credential misuse and insider risk• Role-based permissions and audit trails• Supports compliance and governance |
Tradeoffs | • Does not address payment fraud or external threats• Complex to implement across legacy systems• Requires ongoing user management discipline |
When It’s the Wrong Fit | • Small hotels with simple operations• Teams focused primarily on fraud prevention |
Unified Security & Risk Platforms
These platforms combine fraud detection, data protection, and threat monitoring into a single system.
Best for enterprise hotel groups and portfolios seeking centralized oversight across properties. Typically involves cross-functional ownership.
Category | Details |
|---|---|
Definition | Comprehensive platforms that combine fraud detection, data protection, and threat monitoring into a single system |
Typical Buyer | CIO, IT Director, Finance + Operations leadership |
Best Fit Properties | Enterprise hotel groups, management companies, multi-property portfolios |
Strengths | • Holistic view of risk across the organization• Reduces tool fragmentation• Enables coordinated incident response• Scales across multiple properties |
Tradeoffs | • Higher cost and longer implementation• Requires alignment across teams• May exceed needs of smaller properties |
When It’s the Wrong Fit | • Independent hotels with limited complexity• Operators looking for a narrow, quick solution |
How to choose the right type
Choosing the right type comes down to aligning the solution with your primary risk exposure and internal capabilities. Hotels with high transaction volume should prioritize payment-focused fraud tools, while those with complex IT environments need stronger infrastructure protection.
Larger portfolios may benefit from unified platforms, but only if they have the internal resources to support them. In practice, the right choice depends less on feature breadth and more on how well the system aligns with your team structure, risk profile, and operational complexity.
Cyber security and fraud prevention software acts as a protective layer across a hotel’s digital and financial operations—monitoring transactions, securing systems, and identifying suspicious behavior before it turns into financial loss or a data breach.
Rather than relying on reactive processes or manual audits, these platforms provide continuous, real-time oversight of risk across booking channels, payment flows, staff access, and IT infrastructure. The goal is not just to block threats, but to enable hotels to operate confidently while minimizing friction for guests and staff.
Capability | Description | Operational Value |
|---|---|---|
Transaction Risk Scoring | Analyzes booking and payment data in real time to identify high-risk transactions based on patterns, behavior, and historical fraud signals | Reduces chargebacks and fraudulent bookings while allowing legitimate transactions to proceed smoothly |
Chargeback Prevention & Management | Flags suspicious bookings pre-stay and provides tools to dispute or prevent chargebacks post-transaction | Protects revenue and reduces time spent managing disputes |
Payment Authentication & Tokenization | Supports secure payment methods such as 3D Secure and replaces sensitive card data with tokens | Minimizes exposure to card data breaches and improves compliance with payment standards |
Network & Endpoint Monitoring | Continuously monitors hotel systems, devices, and networks for unusual activity or vulnerabilities | Detects threats like malware or unauthorized access before they impact operations |
User Access Control & Authentication | Manages staff access to systems through permissions, multi-factor authentication, and role-based controls | Reduces risk of internal breaches and unauthorized system access |
Threat Detection & Alerting | Identifies anomalies across systems, bookings, or user behavior and triggers alerts for investigation | Enables faster response to potential security incidents |
Compliance & Audit Logging | Tracks system activity and maintains detailed logs for audits and regulatory requirements | Simplifies compliance with standards like PCI DSS and supports internal accountability |
Automated Response Workflows | Triggers predefined actions such as blocking transactions, locking accounts, or escalating alerts | Reduces reliance on manual intervention and speeds up incident response |
Unlike point solutions that address a single risk area, modern platforms often span both fraud prevention and broader cyber security, creating a more unified view of risk across the operation.
Operationally, these systems function as a background control layer within the hotel’s tech stack. When integrated with booking engines, PMS, payment gateways, and internal systems, they automatically evaluate risk at key moments—such as during a reservation, payment authorization, or staff login—and trigger appropriate actions. This allows hotels to prevent issues proactively while maintaining smooth day-to-day operations and guest experiences.
At a glance, many cyber security and fraud prevention platforms can appear similar. Most vendors claim to offer real-time monitoring, fraud detection, and compliance support, often using similar language around AI, automation, and risk reduction. For hotel operators, this can make it difficult to distinguish between solutions that are truly operationally impactful and those that simply check the right marketing boxes.
In practice, however, these platforms differ significantly in how they perform day to day. The real gap emerges in how effectively a system integrates into hotel workflows, how accurately it detects threats without disrupting operations, and how much manual effort is required from internal teams. A solution that looks strong on paper can still create operational friction if it generates too many false positives or requires constant oversight.
Our evaluation framework focuses on what matters most in a live hotel environment: how well the platform protects revenue, reduces operational burden, and fits into existing systems. This includes assessing integration depth with PMS and payment systems, the level of automation in fraud detection and response, and how clearly the platform surfaces actionable insights for staff.
Ultimately, the goal is to help hoteliers identify solutions that function as true operational safeguards—quietly protecting the business in the background—rather than tools that rely heavily on manual intervention or deliver limited real-world impact.
Evaluation Scorecard
Capability | Importance | What to Ask Vendors | What Good Looks Like | Red Flags / Weak Implementations |
|---|---|---|---|---|
PMS & Booking Engine Integration | ★★★★★ | How does your system integrate with our PMS and booking engine? Is data shared in real time? | Seamless, real-time data exchange with bookings and guest profiles | Batch syncing, manual exports, or limited booking visibility |
Payment Gateway Integration | ★★★★★ | Do you integrate directly with our payment provider? What data do you analyze? | Deep integration with payment flows, enabling real-time fraud checks | поверх-layer integrations with limited transaction data access |
Transaction Risk Scoring Accuracy | ★★★★★ | How do you minimize false positives while catching fraud? | High accuracy with adaptive models that improve over time | Excessive false declines or reliance on static rules |
Automated Fraud Prevention Workflows | ★★★★☆ | What actions are automated vs. manual? Can rules be customized? | Automated blocking, flagging, and escalation with configurable logic | Heavy reliance on manual review or static workflows |
Threat Detection Beyond Payments | ★★★★☆ | Do you monitor for system intrusions or only transaction fraud? | Coverage across user behavior, access patterns, and system anomalies | Limited to payment fraud only |
User Access & Authentication Controls | ★★★★☆ | How do you manage staff access and authentication? | Role-based access, multi-factor authentication, centralized control | Weak access controls or lack of auditability |
Compliance & Data Protection | ★★★★☆ | How do you support PCI DSS and data privacy requirements? | Built-in encryption, tokenization, and audit logs | Partial compliance support or unclear data handling practices |
Alerting & Incident Response | ★★★☆☆ | How are alerts delivered and prioritized? What response tools are included? | Clear, actionable alerts with workflows for investigation and resolution | Alert fatigue, unclear prioritization, or email-only notifications |
Reporting & Risk Analytics | ★★★☆☆ | What reporting is available for fraud trends and security events? | Dashboards that translate data into actionable insights | Static reports with limited operational value |
Ease of Use for Hotel Teams | ★★★☆☆ | Can non-technical staff understand and act on alerts? | Intuitive interface with clear workflows for different roles | Overly technical UI requiring IT intervention for basic tasks |
Dealbreaker Questions
These questions can quickly surface whether a solution is operationally viable or likely to create friction:
Does the platform evaluate transactions in real time before payment authorization?
If fraud checks happen after the fact, hotels remain exposed to chargebacks and revenue loss.
Are fraud prevention actions automated or dependent on manual review?
Solutions that require constant human intervention often fail to scale and increase operational workload.
Does the system integrate directly with both the PMS and payment gateway?
Without deep integrations, risk analysis is incomplete and less effective.
Can alerts be prioritized and acted on within the platform itself?
If teams have to rely on email alerts or external tools, response times slow down and issues can escalate.
These questions help quickly filter out solutions that may look capable on the surface but fall short in real-world hotel operations.
Large Hotels & Resorts
Large hotels and resorts operate highly complex environments with multiple departments, high transaction volume, and significant data exposure across systems. These properties often have dedicated IT teams and must balance strong security controls with uninterrupted guest experiences. Technology plays a critical role not just in protection, but in enabling scale, compliance, and centralized oversight across operations.
Defining Characteristics
High booking and payment volume across multiple channels
Multiple departments and systems (PMS, POS, spa, golf, etc.)
Dedicated IT and security resources
High exposure to compliance and data privacy requirements
Complex network infrastructure and guest-facing systems
Common Needs & Preferences
Requires deep integrations across core systems
Prioritizes centralized control and visibility
Needs advanced automation to reduce manual oversight
Focuses on compliance and audit readiness
Values scalable solutions across properties or brands
Key Features and Needs
Feature Title | Description | Why It’s Critical |
|---|---|---|
Centralized Risk Dashboard | Unified view of fraud, threats, and alerts across systems and properties | Enables corporate teams to monitor and manage risk at scale |
PMS & POS Data Integration | Connects guest, transaction, and operational data across systems | Provides full context for accurate risk detection |
Automated Incident Response | Triggers predefined actions like blocking transactions or locking accounts | Reduces reliance on manual intervention in high-volume environments |
Multi-Property Policy Management | Applies consistent security rules across all properties | Ensures standardized protection and compliance across the portfolio |
Compliance & Audit Tools | Built-in reporting, logging, and controls for regulatory requirements | Supports audits and reduces legal and financial risk |
Boutique & Independent Hotels
Boutique and independent hotels operate with leaner teams and place a strong emphasis on guest experience and brand differentiation. While their risk exposure may be lower in scale, they still face meaningful threats—especially around payment fraud and guest data. These hotels need solutions that protect revenue without adding operational complexity.
Defining Characteristics
Smaller teams with limited or no dedicated IT staff
Strong focus on guest experience and personalization
Moderate online booking volume
Reliance on third-party tools and integrations
Limited tolerance for operational friction
Common Needs & Preferences
Prefers intuitive, easy-to-manage systems
Prioritizes fraud prevention tied to bookings and payments
Needs minimal setup and ongoing management
Values tools that don’t disrupt guest experience
Looks for cost-effective, targeted solutions
Key Features and Needs
Feature Title | Description | Why It’s Critical |
|---|---|---|
Real-Time Booking Fraud Detection | Evaluates reservations as they are made to flag suspicious activity | Prevents fraudulent bookings without impacting legitimate guests |
Payment Authentication Tools | Adds layers like 3D Secure during checkout | Reduces chargebacks while maintaining conversion rates |
Booking Engine Integration | Connects directly to reservation flow for seamless fraud checks | Ensures protection happens at the point of transaction |
Simple Alert Management | Clear, prioritized alerts that non-technical staff can act on | Enables operational teams to respond quickly without IT support |
Low-Touch Deployment | Minimal setup and configuration required | Reduces burden on small teams and speeds time to value |
Small Hotels & B&Bs
Small hotels and B&Bs typically operate with very limited staff and minimal technical expertise. Owners or general managers often handle multiple roles, making simplicity and reliability critical. Security solutions in this segment must work quietly in the background, requiring little to no active management.
Defining Characteristics
Very small teams, often owner-operated
Limited technical knowledge or IT support
Low to moderate booking volume
High reliance on OTAs and simple booking tools
Strong need for operational simplicity
Common Needs & Preferences
Prioritizes ease of use and automation
Needs plug-and-play solutions with minimal setup
Highly sensitive to cost and complexity
Prefers bundled or all-in-one tools
Avoids systems requiring ongoing configuration
Key Features and Needs
Feature Title | Description | Why It’s Critical |
|---|---|---|
Fully Automated Fraud Filtering | Automatically blocks or flags suspicious transactions without manual input | Eliminates need for constant monitoring by small teams |
Pre-Configured Risk Rules | Out-of-the-box fraud settings tailored to hospitality | Reduces setup time and complexity |
Lightweight Payment Integration | Simple connection to existing payment provider | Enables quick deployment without technical overhead |
Passive Monitoring | Runs in the background without requiring daily interaction | Allows operators to focus on core operations |
Transparent Pricing | Clear, predictable pricing with no hidden costs | Aligns with tight budgets and simplifies decision-making |
Budget Hotels, Motels & Limited-Service Properties
Budget and limited-service properties operate with a strong focus on efficiency, cost control, and standardized processes. Staff is often limited, and operations are designed to minimize complexity. Security solutions must align with this model by being cost-effective, automated, and operationally lightweight.
Defining Characteristics
Lean staffing with limited specialization
High focus on operational efficiency
Standardized service model with fewer touchpoints
Moderate transaction volume, often price-sensitive guests
Tight budget constraints
Common Needs & Preferences
Prioritizes cost-effective solutions with clear ROI
Needs automation to reduce staff workload
Prefers simple, standardized workflows
Avoids tools requiring heavy customization
Values fast deployment across properties
Key Features and Needs
Feature Title | Description | Why It’s Critical |
|---|---|---|
Automated Chargeback Reduction | Identifies and prevents high-risk transactions before completion | Protects thin margins from avoidable revenue loss |
Standardized Fraud Rules Engine | Applies consistent fraud filters across all bookings | Ensures efficiency and reduces need for manual oversight |
Fast Payment System Integration | Quick setup with common payment gateways | Enables rapid rollout without operational disruption |
Low-Cost, Scalable Pricing | Pricing model aligned with volume and property size | Keeps costs predictable and aligned with margins |
Centralized Alert Handling (for groups) | Basic dashboard to monitor alerts across multiple properties | Supports small portfolios without adding complexity |
Choosing the right solution ultimately comes down to operational fit. A platform built for enterprise environments may overwhelm a small property, while lightweight tools may fall short in complex, multi-system operations. The key is to align the solution with your team structure, risk exposure, and day-to-day workflows—ensuring the technology supports the business rather than adding unnecessary complexity.
Best Cyber Security & Fraud Prevention Software by Property Type
These rankings are driven by real-world performance data—not vendor claims. By analyzing verified hotel reviews, product adoption trends, and usage patterns across different property types, we identify which cyber security and fraud prevention solutions consistently deliver results in live hotel environments. The outcome is a set of recommendations grounded in operational fit—helping you find the platforms that work best for hotels with similar risk profiles, team structures, and levels of complexity.
Best for Branded Hotels
Canary Digital Authorizations is rated 97% by 1086 Branded Hotels
Best for Boutique Hotels
Canary Digital Authorizations is rated 96% by 906 Boutique Hotels
Best for Bed & Breakfast & Inns
Canary Digital Authorizations is rated 96% by 817 Bed & Breakfast & Inns
Best for Luxury Hotels
Canary Digital Authorizations is rated 96% by 716 Luxury Hotels
Best for Airport/Conference Hotels
Canary Digital Authorizations is rated 96% by 687 Airport/Conference Hotels
Best for Limited Service & Budget Hotels
Canary Digital Authorizations is rated 97% by 585 Limited Service & Budget Hotels
Best for Resorts
Canary Digital Authorizations is rated 96% by 555 Resorts
Best for City Center Hotels
Canary Digital Authorizations is rated 96% by 509 City Center Hotels
Best for Extended Stay & Serviced Apartments
Canary Digital Authorizations is rated 97% by 215 Extended Stay & Serviced Apartments
Best for Hostels
Canary Digital Authorizations is rated 94% by 151 Hostels
Best for Motels
Canary Digital Authorizations is rated 98% by 96 Motels
Best for Casinos
Canary Digital Authorizations is rated 98% by 85 Casinos
Best for RV Parks & Campgrounds
Canary Digital Authorizations is rated 94% by 49 RV Parks & Campgrounds
Best for Vacation Rentals & Villas
Canary Digital Authorizations is rated 97% by 28 Vacation Rentals & Villas
How to Choose the Right Cyber Security & Fraud Prevention Software Provider
This list is already tailored to your hotel’s size, type, and operational complexity. Want to refine it further? Use the filters to narrow your shortlist by region, property profile, and existing tech stack to see which cyber security and fraud prevention solutions best align with your specific risk exposure and system environment.
Cyber Security & Fraud Prevention Software Features & Comparison
Discover popular comparisons
Best Hotel Cyber Security & Fraud Prevention Reviews
Everything You Need to Know About Cyber Security & Fraud Prevention Software
Not sure where to start with cyber security and fraud prevention for your hotel? This section is your practical crash course. We’ll break down what these solutions actually do, how they protect both revenue and guest data, and which capabilities matter most in a hotel environment—from payment fraud prevention to system-wide threat monitoring.
You’ll also learn how pricing typically works, which integrations are critical (like PMS and payment gateways), and what to expect during setup and ongoing use. We’ll cover the operational benefits, common pitfalls to avoid, and key trends shaping how hotels manage risk today. It’s everything you need to get oriented—grounded in real-world insights from hoteliers managing these challenges every day.
What is Cyber Security & Fraud Prevention Software
Cyber security and fraud prevention software for hotels is a category of technology designed to protect hotel operations from financial loss, data breaches, and unauthorized access across their digital ecosystem.
At its core, these platforms monitor and analyze activity across booking systems, payment transactions, staff access, and IT infrastructure to identify suspicious behavior in real time. This includes preventing fraudulent reservations and chargebacks, securing guest payment data, and detecting potential threats like account takeovers or system intrusions.
Operationally, the software acts as a continuous risk management layer embedded within the hotel’s tech stack. By integrating with systems like the PMS, booking engine, and payment gateway, it can evaluate risk at key moments—such as when a reservation is made, a payment is processed, or a staff member logs into a system—and automatically take action when needed.
For hotels, the value is twofold: protecting revenue by reducing fraud and chargebacks, and safeguarding guest trust by ensuring sensitive data is secure. Rather than relying on manual checks or reactive processes, these solutions help hotels proactively manage risk while maintaining smooth, uninterrupted operations.
Key Features to Look For in Cyber Security & Fraud Prevention Software
Cyber security and fraud prevention tools in hospitality have evolved from reactive safeguards into continuous, real-time protection layers embedded across hotel operations. What was once limited to basic payment security now spans transaction monitoring, user access control, and system-wide threat detection—reflecting the growing complexity of hotel tech stacks and the rise in digital risk exposure.
In practice, these features matter because they directly impact revenue protection, operational workload, and guest trust. A well-configured system can prevent fraudulent bookings before they occur, reduce chargeback disputes, and minimize the need for manual oversight. At the same time, it ensures that legitimate guests move through booking and payment flows without friction.
Modern platforms also play a critical role in connecting data across systems. By integrating with PMS, payment gateways, and internal tools, they enable more accurate risk detection, automate response workflows, and provide visibility into where threats are emerging—helping hotel teams stay proactive rather than reactive.
Feature Evaluation Table
Capability Area | Feature | Description |
|---|---|---|
Fraud Prevention & Revenue Protection | Real-Time Transaction Scoring | Evaluates each booking or payment as it happens using behavioral and historical data, helping block fraudulent transactions before they are completed. |
Chargeback Prevention Tools | Identifies high-risk bookings pre-stay and provides documentation or automation to reduce and dispute chargebacks. | |
Payment Authentication (e.g., 3D Secure) | Adds an extra verification step during payment to confirm cardholder identity and reduce fraud exposure. | |
Card Tokenization | Replaces sensitive card data with secure tokens, reducing the risk of data breaches and simplifying compliance. | |
Custom Fraud Rules Engine | Allows hotels to define rules based on booking patterns, geolocation, or guest behavior to flag suspicious activity. | |
Security & Threat Detection | Network & Endpoint Monitoring | Continuously scans hotel systems and devices for unusual activity, helping detect malware or unauthorized access early. |
User Behavior Monitoring | Tracks login patterns and system usage to identify anomalies that may indicate compromised accounts. | |
Threat Detection & Alerting | Generates alerts when suspicious activity is detected across systems, enabling faster investigation and response. | |
Multi-Factor Authentication (MFA) | Requires additional verification for system access, reducing the risk of credential theft and unauthorized entry. | |
Role-Based Access Control | Limits system access based on staff roles, ensuring employees only access the data and tools they need. | |
Operations & Workflow Automation | Automated Response Workflows | Triggers actions like blocking transactions or locking accounts based on predefined risk conditions, reducing manual intervention. |
Alert Prioritization & Routing | Categorizes and routes alerts to the appropriate team or role, improving response times and reducing noise. | |
Centralized Security Dashboard | Provides a single view of threats, transactions, and system activity for easier monitoring and decision-making. | |
Incident Logging & Audit Trails | Records all actions and events for internal tracking and compliance, supporting investigations and audits. | |
Integrations & Data | PMS Integration | Connects guest and reservation data to improve context for fraud detection and ensure alignment with hotel operations. |
Payment Gateway Integration | Enables direct access to transaction data for real-time fraud analysis and authentication workflows. | |
API & Third-Party Integrations | Allows connection with CRM, booking engines, and other systems to create a more complete risk profile. | |
Reporting & Risk Analytics | Provides insights into fraud trends, system vulnerabilities, and operational impact, helping teams make informed decisions. |
These capabilities separate basic tools from more operationally integrated platforms. While many solutions offer some level of fraud detection or security monitoring, the real differentiator lies in how well these features work together—automating protection, reducing manual effort, and embedding seamlessly into daily hotel workflows.
- Penetration testing
- Threat lifecycle management
- Managed WAN security platform
- Network security
- Penetration testing
- Threat lifecycle management
- Managed WAN security platform
- Network security
- PCI compliance audit
- Compliance readiness
- PCI compliance audit
- Compliance readiness
- Security Information and Event Management (SIEM)
- Security Information and Event Management (SIEM)
What are the benefits of Cyber Security & Fraud Prevention Software?
In today’s hotel environment, more revenue and guest data flows through digital systems than ever before—making cyber security and fraud prevention a direct operational priority, not just an IT concern. The biggest benefits come down to two things: protecting revenue and reducing operational risk. But the impact goes deeper when you look at how these systems support day-to-day hotel operations.
Fraud is one of those issues that often goes unnoticed—until it becomes expensive. Chargebacks, fraudulent bookings, and payment disputes can quietly erode margins over time, especially for hotels with high online booking volume. A strong fraud prevention system stops these issues at the source by identifying high-risk transactions before they’re confirmed. That means fewer disputes, less revenue leakage, and less time spent by teams investigating and responding to issues after the fact.
At the same time, these platforms help protect one of your most valuable assets: guest trust. Hotels handle sensitive data every day, from payment details to personal information. Security breaches or unauthorized access don’t just create financial risk—they can damage reputation and guest confidence. By securing systems, controlling access, and monitoring activity, these solutions help ensure that guest data is handled safely across every touchpoint.
Beyond protection, there’s also a clear operational benefit. Without the right tools, teams often rely on manual checks, reactive processes, or fragmented systems to manage risk. This creates inefficiencies and increases the chance of human error. Modern platforms automate many of these workflows—flagging suspicious activity, triggering actions, and centralizing alerts—so teams can focus on core operations instead of constantly monitoring for issues.
Finally, as hotel tech stacks become more interconnected, cyber security and fraud prevention software plays a key role in keeping everything running smoothly. From PMS and payment systems to booking engines and internal tools, these platforms act as a control layer that ensures systems are used securely without slowing down operations. The result is a more resilient, efficient operation that can scale confidently without increasing exposure to risk.
Critical Integrations for Cyber Security & Fraud Prevention Software
When evaluating cyber security and fraud prevention software, it’s easy to focus on features like threat detection or fraud scoring. But in practice, the effectiveness of any solution depends heavily on how well it connects to your existing systems. Without the right integrations, even the most advanced tools are working with incomplete data—and that leads to missed threats or unnecessary friction.
At a minimum, your solution should be tightly connected to the systems where risk actually occurs:
PMS for access to guest profiles, reservations, and operational context
Booking Engine to evaluate reservations at the point of creation
Payment Gateway to analyze transactions in real time and trigger authentication workflows
User Authentication / Identity Systems to monitor and control staff access
These integrations shouldn’t rely on manual data transfers or delayed syncing. The more native or deeply embedded they are, the more accurate and timely your risk detection will be. If a platform sits outside your core workflows or only receives partial data, it limits its ability to act proactively.
Once these foundational integrations are in place, the next layer of value comes from how well the platform connects to the broader ecosystem—helping you unify data, automate workflows, and gain visibility across both financial and operational risk.
Pricing in this category is typically SaaS-based, but it often includes a mix of subscription fees and usage-based components depending on how the platform is deployed. Some vendors charge a fixed monthly fee per property, while others price based on transaction volume, number of users, or level of protection required. In many cases, pricing scales with how deeply the solution is integrated into booking, payment, and IT systems.
Hotels should look beyond the base subscription and evaluate total cost of ownership. This includes integration setup, ongoing support, and any additional modules for advanced fraud detection or compliance. For properties with complex tech stacks or multiple systems, integration costs can be a meaningful factor.
Scalability is another key consideration. A solution that works for a single property may become significantly more expensive when rolled out across a portfolio, especially if pricing is tied to transaction volume or system usage. Understanding how pricing evolves as your operation grows is critical to making the right long-term decision.
Common Pricing Models
Pricing Model | How It Works | Typical Cost Considerations |
|---|---|---|
Per-Property Subscription | Flat monthly or annual fee per hotel property | Predictable costs, but may increase with added features or modules |
Transaction-Based Pricing | Fees based on number or value of bookings/payments analyzed | Costs scale with booking volume, which can impact margins during high-demand periods |
Tiered SaaS Plans | Different pricing tiers based on feature access or usage limits | Lower tiers may lack advanced automation or integrations needed for larger operations |
Per-User Licensing | Pricing based on number of staff accessing the platform | Costs increase as more departments or roles require access |
Enterprise / Portfolio Pricing | Custom pricing for multi-property groups based on scale and complexity | Can offer cost efficiencies at scale but often requires negotiation and longer contracts |
Implementation & Integration Fees | One-time setup costs for connecting PMS, payment gateways, and other systems | Higher for properties with complex tech stacks or multiple integrations |
What Impacts Pricing the Most
Property size and transaction volume, since more bookings and payments require greater processing and monitoring capacity
Integration complexity, as connecting multiple systems like PMS, payment gateways, and internal tools increases setup effort
Feature depth and automation level, with advanced fraud detection, automation, and reporting typically priced at a premium
Number of properties or users, especially for multi-property groups scaling the solution across portfolios
Evaluating ROI
When evaluating ROI, hotels should focus on how effectively the solution reduces fraud-related losses, minimizes chargebacks, and lowers the operational burden on staff. The most valuable platforms not only protect revenue but also automate risk management processes, allowing teams to focus on core operations. Over time, the right solution should pay for itself through avoided losses and improved efficiency.
Successful implementation of cyber security and fraud prevention software depends less on installation and more on how well the platform is embedded into your existing workflows and systems. The most effective vendors clearly map out the onboarding process upfront, outlining integration requirements, data access needs, and the roles your team will play in configuring rules, permissions, and response workflows.
Hotels should expect close coordination between internal stakeholders—typically IT, Finance, and Operations—during implementation. Key steps include connecting to core systems like the PMS, booking engine, and payment gateway, configuring fraud rules and authentication settings, and aligning alerting workflows with internal processes. Clear ownership on both the hotel and vendor side is critical to avoid gaps in coverage.
Implementation timelines vary based on complexity. Smaller properties with standard integrations can typically be up and running within 2–3 weeks, while larger hotels or multi-property groups with more systems and stricter compliance requirements should plan for 4–6+ weeks. Investing time upfront in proper configuration ensures the system runs effectively in the background—reducing risk without adding operational friction.
The Future of Cyber Security & Fraud Prevention Software
Traditional fraud prevention relied heavily on manual reviews and static rules. Today’s platforms are moving toward real-time decisioning, where every transaction and interaction is evaluated instantly using dynamic risk models.
This shift allows hotels to stop fraudulent bookings before they are confirmed, rather than dealing with chargebacks after the fact. Automation also reduces the operational burden on teams, eliminating the need for constant monitoring and manual intervention.
Here’s what this means for your hotel:
Fewer chargebacks and revenue losses. Real-time transaction scoring blocks high-risk bookings at the source, reducing post-stay disputes and financial leakage.
Lower operational workload. Automated decisioning replaces manual review processes, allowing teams to focus on higher-value tasks.
Better guest experience. Legitimate bookings move through payment flows without unnecessary friction or delays.
Historically, payment fraud and IT security were managed separately. That line is quickly disappearing as platforms begin to unify financial fraud detection with broader system and data protection.
Modern solutions now monitor not just transactions, but also user behavior, system access, and network activity—creating a more complete view of risk across the hotel operation. This convergence is especially important as attacks increasingly span multiple vectors, from stolen payment data to compromised staff credentials.
Here’s what this means for your hotel:
Holistic risk visibility. Hotels can monitor financial and operational threats from a single platform instead of managing siloed tools.
Stronger protection against complex attacks. Linking payment data with user activity helps identify patterns that would otherwise go unnoticed.
Simplified tech stack. Fewer standalone tools reduce integration challenges and streamline security management.
As hotel systems become more interconnected, cyber security and fraud prevention platforms are embedding more deeply into core operational systems like PMS, booking engines, and payment gateways.
This deeper integration enables more accurate risk detection by combining data from multiple sources in real time. It also allows platforms to trigger actions directly within workflows—such as blocking a transaction during booking or restricting access at login.
Here’s what this means for your hotel:
More accurate fraud detection. Access to real-time booking, payment, and guest data improves risk scoring and reduces false positives.
Seamless operational workflows. Security actions happen within existing systems, avoiding disruption to staff or guests.
Stronger foundation for automation. Integrated systems enable end-to-end workflows, from detection to response, without manual handoffs.
Hoteliers Also Ask
Many modern platforms extend beyond payment fraud to monitor staff access, login behavior, and system usage. This helps identify risks like unauthorized access or misuse of credentials. However, not all solutions offer this capability, so hotels should confirm whether internal risk monitoring is included or requires additional tools.
The key is using systems that evaluate risk in real time without adding friction to low-risk transactions. Strong platforms apply additional verification only when needed, rather than forcing every guest through extra steps. This helps reduce fraud while preserving conversion rates and avoiding unnecessary booking abandonment.
A common mistake is choosing based solely on feature lists rather than operational fit. Hotels may also underestimate the importance of integration depth or select tools that require more manual management than their team can support. Misalignment between the platform and internal workflows often leads to underutilization.
Even smaller properties are exposed to payment fraud and chargebacks, especially with online bookings. While their needs may be simpler, having basic protection in place can prevent revenue loss and reduce manual oversight. The key is choosing a solution that is easy to manage and proportionate to the property’s complexity.
Success is typically measured through reduced chargebacks, fewer fraudulent bookings, and lower manual review workload. Over time, hotels should also see improved approval rates for legitimate transactions and better visibility into risk trends, allowing for more informed operational decisions.
Ownership often depends on the primary use case. Payment-focused tools are usually managed by Finance or Revenue teams, while broader security platforms fall under IT. In many cases, effective use requires collaboration across departments, especially when fraud prevention and system security overlap.
These systems act as a protective layer across existing tools rather than replacing them. They sit alongside PMS, booking engines, and payment systems, analyzing activity and enforcing security controls. Their effectiveness depends on how well they connect to these systems and operate within existing workflows.
Rule-based systems rely on fixed conditions (e.g., location or booking value), which can be effective but require ongoing manual tuning. AI-driven models analyze patterns across large datasets and adapt over time, improving accuracy. In practice, many hotels benefit from a hybrid approach that combines configurable rules with adaptive learning.
This varies widely by platform. Some require ongoing rule tuning and manual review of flagged transactions, while others automate most decisions. Hotels with limited staff should prioritize systems that minimize daily intervention, while larger teams may prefer more control over how risk is evaluated and handled.
LAST UPDATED
APPS TESTED
CONTRIBUTING EXPERTS
Get personalized product recommendations
Product recommendations advisor